Container Security Policy Template
Container Security Policy Template - If this is your first policy, click +. Adapt existing information security policies for cloud. Learn the five key components of container security in our essential guide Web up to 20% cash back open the trend micro cloud one console and select container security. Get access to our collection of 2,000+ business & legal document templates. Web csi consists of four core elements: Web in general, continuous container security for the enterprise is about: Web software factory and ecosystem; Testing features can help you develop security policies, simulate attacks. Web create an aci container group arm template in this tutorial, you deploy a hello world application that generates a hardware attestation report.
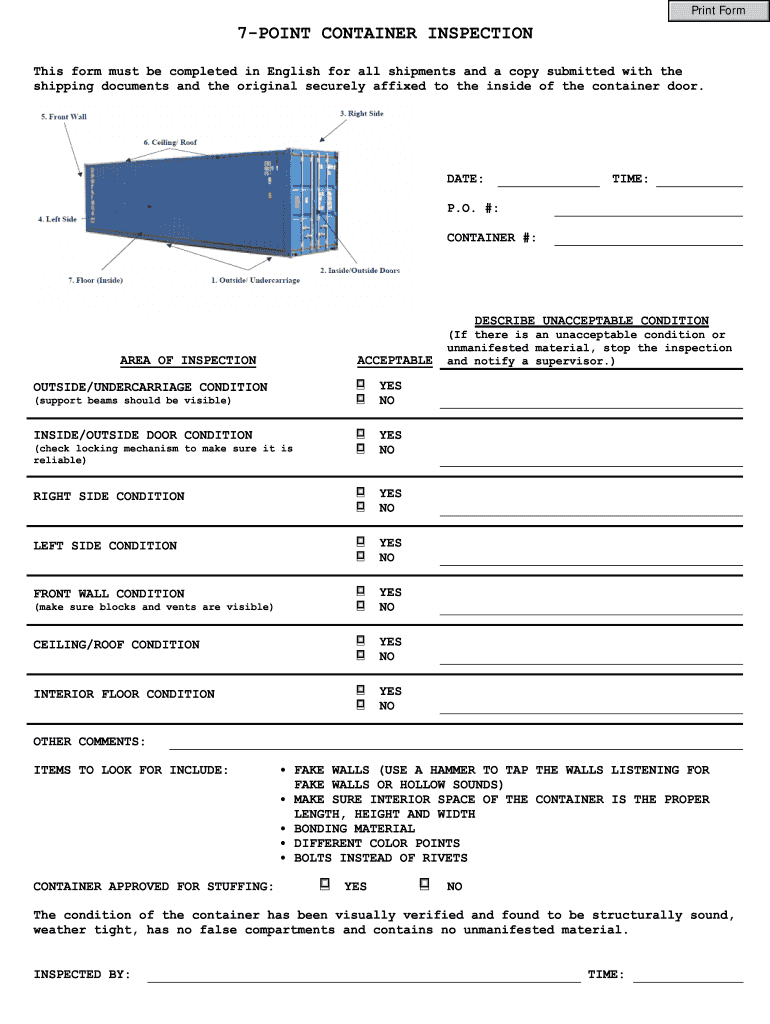
CTPAT 7Point Container Seal Inspection Checklist Door Wall
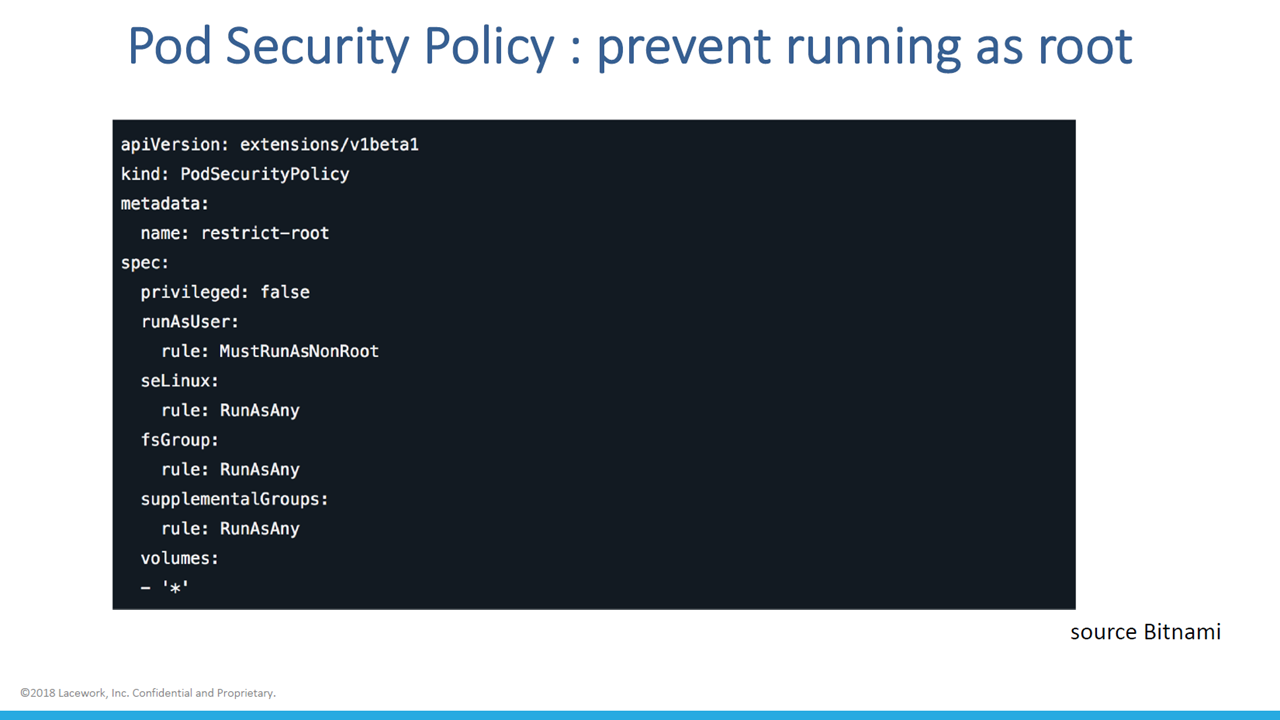
Web the pod security standards define three different policies to broadly cover the security spectrum. Securing the container pipeline and the application; Ad make your free online customized information security policy. Adapt existing information security policies for cloud. Learn the five key components of container security in our essential guide
Improving Security for Deployments at Scale Altoros
Learn the five key components of container security in our essential guide Generally, virtual machines are prevented from. Web the pod security standards define three different policies to broadly cover the security spectrum. Go to the policies page. Web gitlab’s 2022 global devsecops survey found that only 64% of security professionals had a security plan for containers, and many devops.
Container Checklist
Web create an aci container group arm template in this tutorial, you deploy a hello world application that generates a hardware attestation report. Introduces the dod enterprise devsecops container service that provides hardened devsecops tools and deployment templates. Web csi consists of four core elements: Web up to 20% cash back open the trend micro cloud one console and select.
Container Inspection Checklist (Sign off)_word文档免费下载_文档大全
Web container security consultants can use this entirely editable deck to highlight the significance of this process in mitigating risks and reducing vulnerabilities when. Ad explore modern container security solutions to build scalable containerized applications. Securing the container pipeline and the application; Web create an aci container group arm template in this tutorial, you deploy a hello world application that.
SECURING SECURITY CONTAINERS
Web container security consultants can use this entirely editable deck to highlight the significance of this process in mitigating risks and reducing vulnerabilities when. Go to the policies page. Web up to 20% cash back open the trend micro cloud one console and select container security. Easily create your business document and get attorney document review for free. Web create.
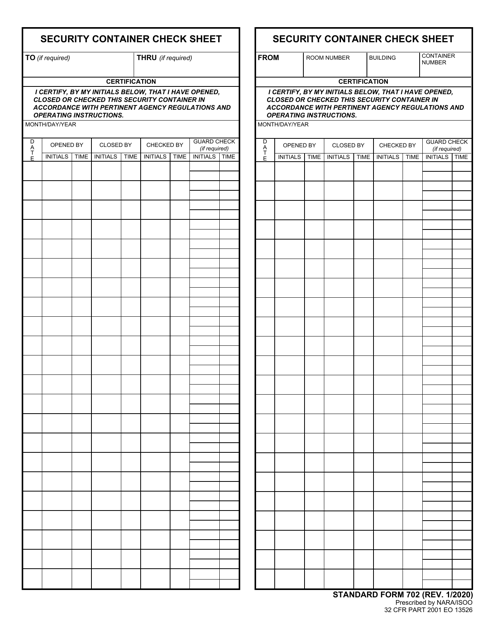
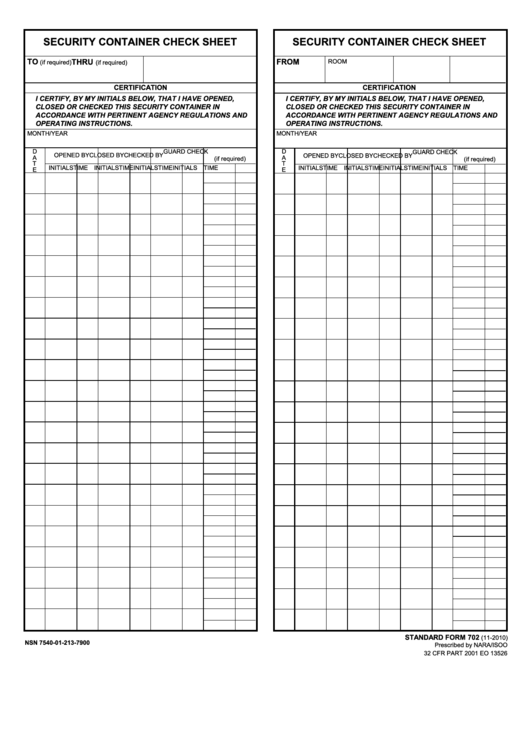
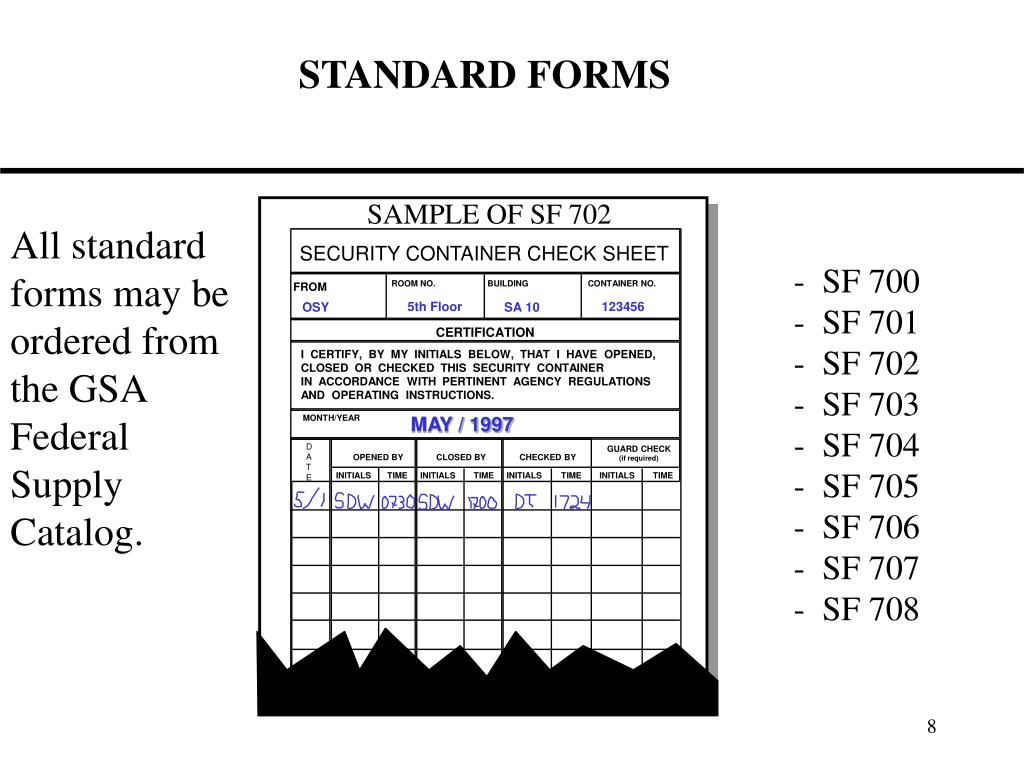
Form SF702 Download Fillable PDF or Fill Online Security Container
Containers represent the next generation of virtualization technology for cloud environments. The following examples show container policies that are constructed for different user groups. Get access to our collection of 2,000+ business & legal document templates. Web up to 20% cash back open the trend micro cloud one console and select container security. Ad make your free online customized information.
SF 702 Security Container Check Sheet Security Checks Matter
Web up to 20% cash back open the trend micro cloud one console and select container security. Following traditional software development methods, developers had to deal with os and application dependencies. Testing features can help you develop security policies, simulate attacks. Web csi consists of four core elements: Get access to our collection of 2,000+ business & legal document templates.
Fillable Security Container Check Sheet Security Container Check Sheet
Unfortunately, containers themselves introduce a new set of security. Web enable constraints and constraint templates. Web in general, continuous container security for the enterprise is about: Security context settings include, but are not limited to: Do one of the following:
PPT NATIONAL SECURITY INFORMATION ANNUAL CONTAINER INSPECTION
Learn the five key components of container security in our essential guide Do one of the following: Web container security consultants can use this entirely editable deck to highlight the significance of this process in mitigating risks and reducing vulnerabilities when. Get access to our collection of 2,000+ business & legal document templates. Adapt existing information security policies for cloud.
Container Inspection Checklist Pdf Fill Online, Printable, Fillable
Ad explore modern container security solutions to build scalable containerized applications. If this is your first policy, click +. Introduces the dod enterprise devsecops container service that provides hardened devsecops tools and deployment templates. Following traditional software development methods, developers had to deal with os and application dependencies. Web enable constraints and constraint templates.
Learn the five key components of container security in our essential guide Ad make your free online customized information security policy. Web in general, continuous container security for the enterprise is about: Web container security consultants can use this entirely editable deck to highlight the significance of this process in mitigating risks and reducing vulnerabilities when. Web up to 20% cash back open the trend micro cloud one console and select container security. Introduces the dod enterprise devsecops container service that provides hardened devsecops tools and deployment templates. Unfortunately, containers themselves introduce a new set of security. Ad explore modern container security solutions to build scalable containerized applications. Web software factory and ecosystem; The following examples show container policies that are constructed for different user groups. Adapt existing information security policies for cloud. Web november 23, 2021 how do containers work? This page shows you how to. Testing features can help you develop security policies, simulate attacks. Web in the last post, i was considering changes i need to make to my repository and code if i want to reuse single templates for my lambda function, role, and policy. Learn the five key components of container security in our essential guide Do one of the following: Web a security context defines privilege and access control settings for a pod or container. Get access to our collection of 2,000+ business & legal document templates. Securing the container pipeline and the application;