Nist Acceptable Use Policy Template
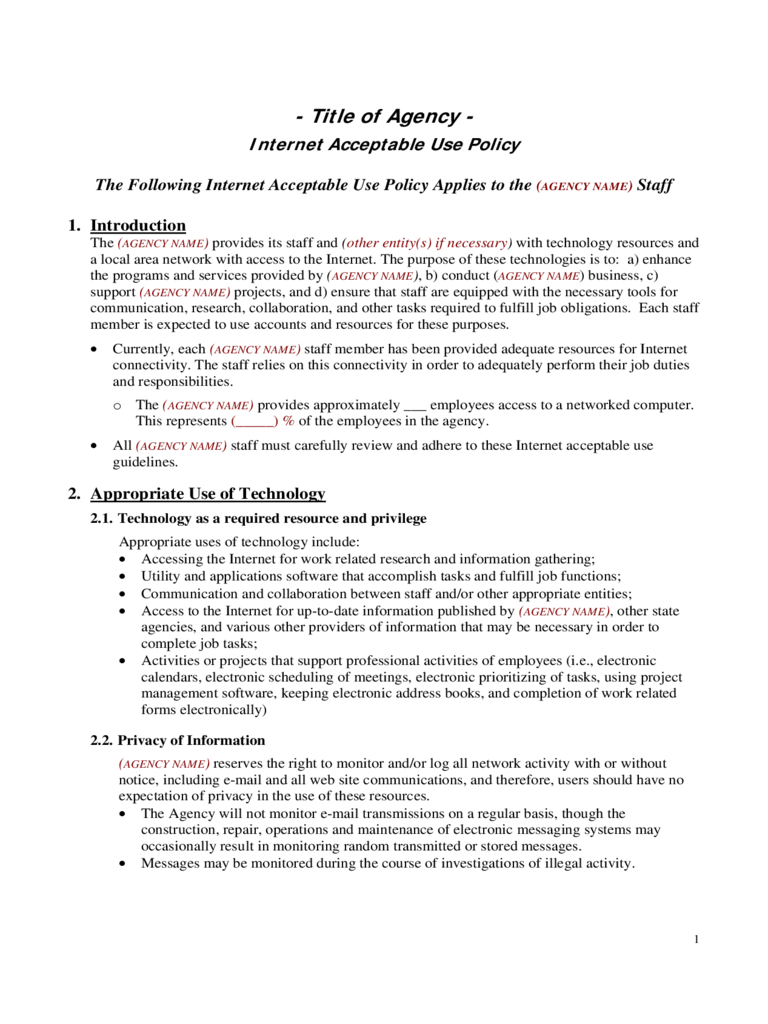
Nist Acceptable Use Policy Template - Web the draft update, which nist has released for public comment, reflects changes in the cybersecurity landscape and makes it easier to put the csf into practice. Web acceptable use policy document this paper provides an example of an acceptable use policy for information resources. This template can assist an enterprise in developing acceptable use for the cis controls. Web the policy templates are provided courtesy of the state of new york and the state of california. The templates can be customized and used as an outline of an organizational. Ad make your free online customized information security policy. Web information security in any organization is largely dependent on the quality of the security policy and the processes that an organization imposes on itself, including policy. Ad download your email & internet usage policy statement and access all our 2,000+ templates. Web nist csf compliance templates. Web access and use policy for the nist‐guest network users of devices connecting to nist‐guest will require acceptance of access and use rules.
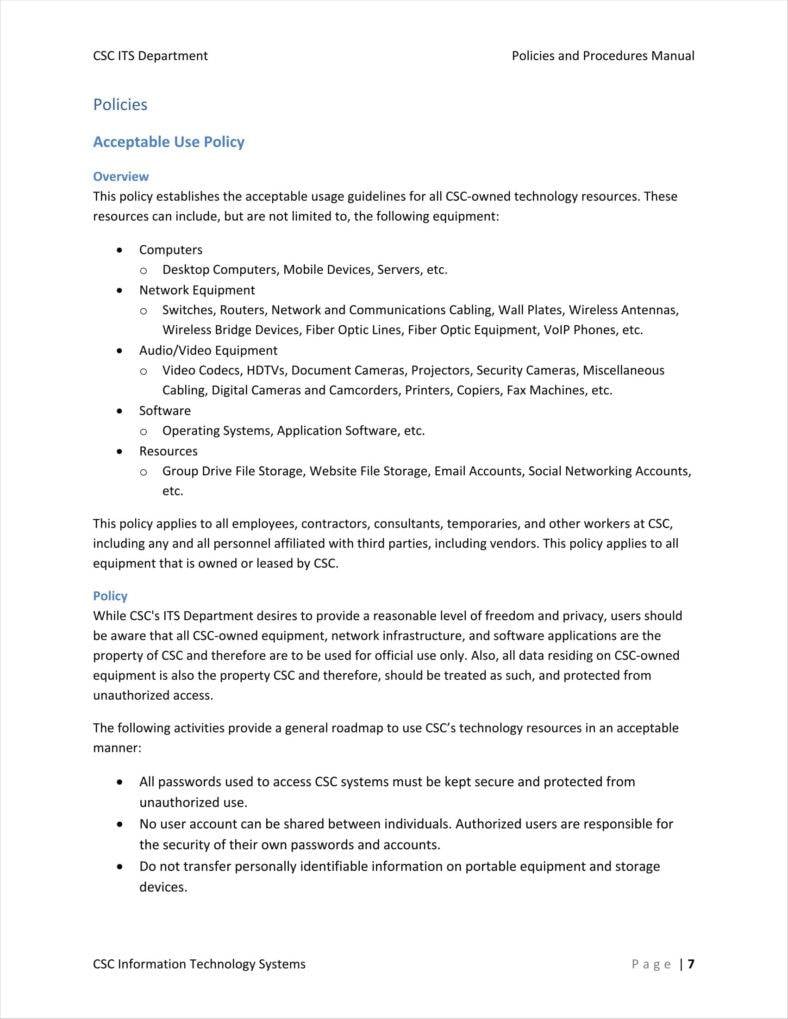
How to define an Acceptable Use IT CyberSecurity Standard? Download
Web revision 1 managing the security of information exchanges kelley dempsey victoria pillitteri andrew regenscheid computer security division information technology. The access and use rules. Approaches, methodologies, implementation guides, mappings to the framework, case studies,. Web acceptable use policy document this paper provides an example of an acceptable use policy for information resources. Acceptable use of nist information technology resources.
Nist Information Security Policy Template
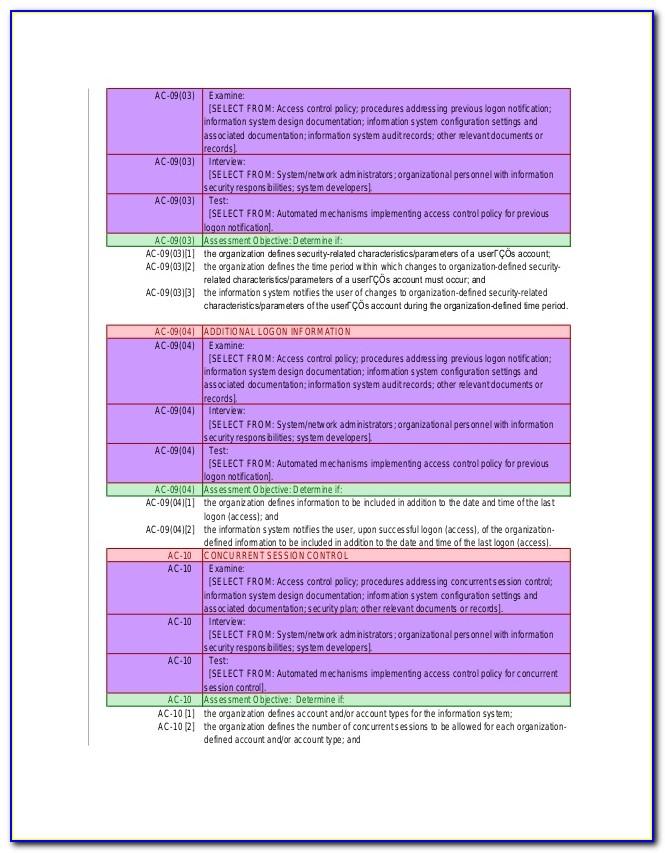
Rules of behavior control statement establish and provide to individuals requiring access to the system,. Web the draft update, which nist has released for public comment, reflects changes in the cybersecurity landscape and makes it easier to put the csf into practice. Telecommuting), which is the ability for an organization’s employees, contractors,. Web revision 1 managing the security of information.
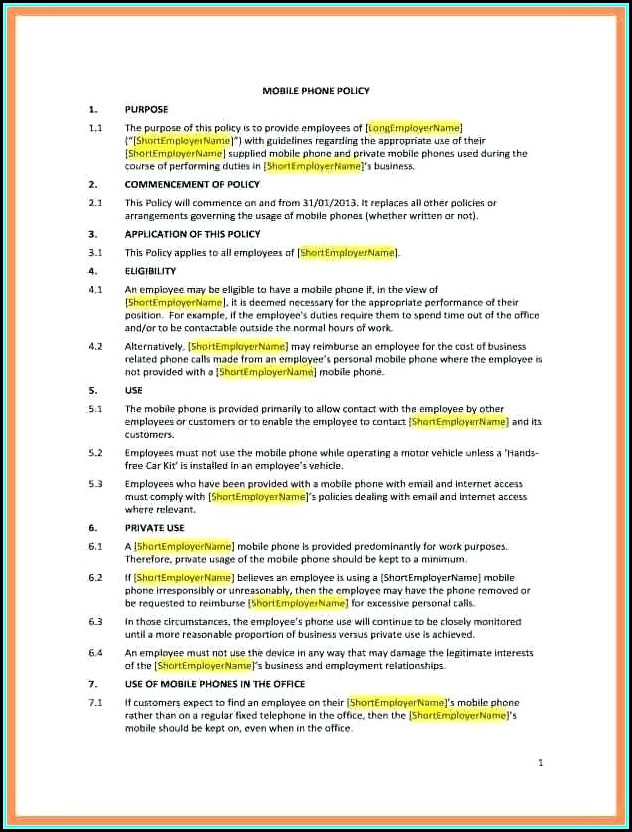
2022 Acceptable Use Policy Template Fillable, Printable PDF & Forms
Web revision 1 managing the security of information exchanges kelley dempsey victoria pillitteri andrew regenscheid computer security division information technology. Web the policy templates are provided courtesy of the state of new york and the state of california. This template can assist an enterprise in developing acceptable use for the cis controls. The templates can be customized and used as.
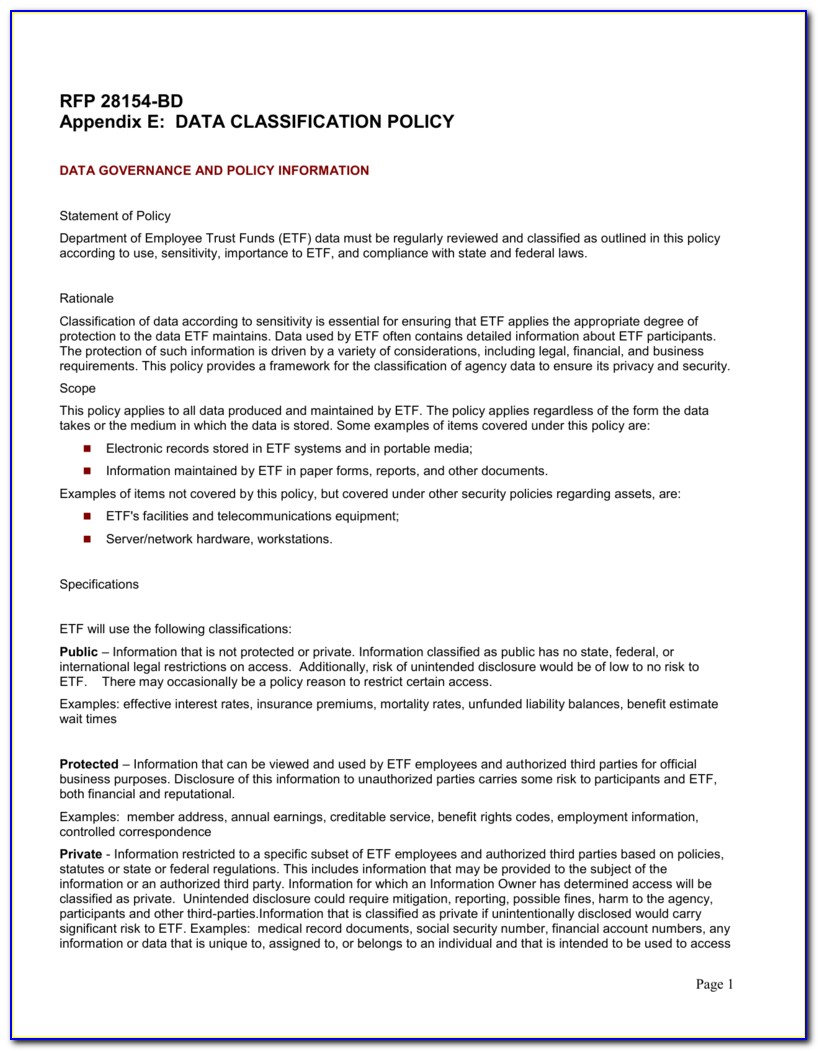
Data Classification Policy Template Nist
3.3.5, 3.6.1, 3.6.2, 3.6.3, 3.13.14. Rules of behavior control statement establish and provide to individuals requiring access to the system,. Ad download your email & internet usage policy statement and access all our 2,000+ templates. Web nist pubs supercedes publication user's guide to securing external devices for telework and remote access download paper. Web acceptable use policy document this paper.
Nist Information Security Policy Template merrychristmaswishes.info
April 2010 author (s) erika mccallister (nist), tim grance (nist), karen scarfone (nist) abstract the purpose of this document is to assist. Web acceptable use policies outline what is appropriate and what is inappropriate when it comes to using the organization’s network and the internet. Web the draft update, which nist has released for public comment, reflects changes in the.
Acceptable Use Policy Template 2019 Policy template, Positive work
Resources include, but are not limited to: Web the following guidelines apply to all who use and access nist information technology resources. Web the draft update, which nist has released for public comment, reflects changes in the cybersecurity landscape and makes it easier to put the csf into practice. Web sans has developed a set of information security policy templates..
Nist Access Control Policy Template
This template can assist an enterprise in developing acceptable use for the cis controls. Web acceptable use policy document this paper provides an example of an acceptable use policy for information resources. Web nist pubs supercedes publication user's guide to securing external devices for telework and remote access download paper. Ad download your email & internet usage policy statement and.
Information Technology Acceptable Use Policy Template technology
Approaches, methodologies, implementation guides, mappings to the framework, case studies,. Rules of behavior control statement establish and provide to individuals requiring access to the system,. The protection of controlled unclassified information (cui) resident in nonfederal systems and organizations is of paramount importance to federal. This template can assist an enterprise in developing acceptable use for the cis controls. Ad make.
Nist Security Plan Template Template 1 Resume Examples MZe12Xo3jx
Resources include, but are not limited to: Web o notional templates developed that organizations can use or adapt for creating their profiles and action plans. This template can assist an enterprise in developing acceptable use for the cis controls. Web nist pubs supercedes publication user's guide to securing external devices for telework and remote access download paper. April 2010 author.
Fantastic Acceptable Use Policy Template Policy template, Templates
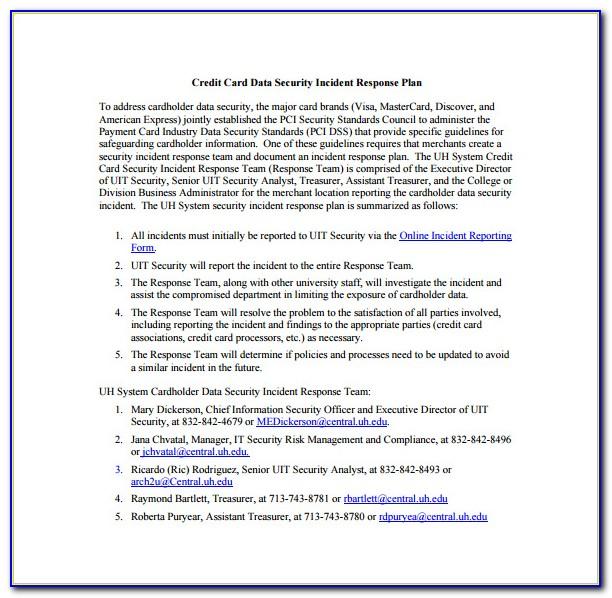
Resources include, but are not limited to: By raymond landolo june 12, 2001. The national institute of standards technology (nist) cybersecurity framework provides a policy framework of computer security guidance. Web revision 1 managing the security of information exchanges kelley dempsey victoria pillitteri andrew regenscheid computer security division information technology. Web the security response plan mentioned earlier is appropriate evidence.
Web the draft update, which nist has released for public comment, reflects changes in the cybersecurity landscape and makes it easier to put the csf into practice. The protection of controlled unclassified information (cui) resident in nonfederal systems and organizations is of paramount importance to federal. 3.3.5, 3.6.1, 3.6.2, 3.6.3, 3.13.14. Approaches, methodologies, implementation guides, mappings to the framework, case studies,. Resources include, but are not limited to: Telecommuting), which is the ability for an organization’s employees, contractors,. The access and use rules. Web the following guidelines apply to all who use and access nist information technology resources. Ad download your email & internet usage policy statement and access all our 2,000+ templates. Web access and use policy for the nist‐guest network users of devices connecting to nist‐guest will require acceptance of access and use rules. This template can assist an enterprise in developing acceptable use for the cis controls. Easily create your business document and get attorney document review for free. Acceptable use of nist information technology resources. April 2010 author (s) erika mccallister (nist), tim grance (nist), karen scarfone (nist) abstract the purpose of this document is to assist. Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program. Web sans has developed a set of information security policy templates. Web the policy templates are provided courtesy of the state of new york and the state of california. Web the security response plan mentioned earlier is appropriate evidence for several controls: Users with multiple accounts (as defined in 3.1.4 and 3.1.5) must. Web o notional templates developed that organizations can use or adapt for creating their profiles and action plans.