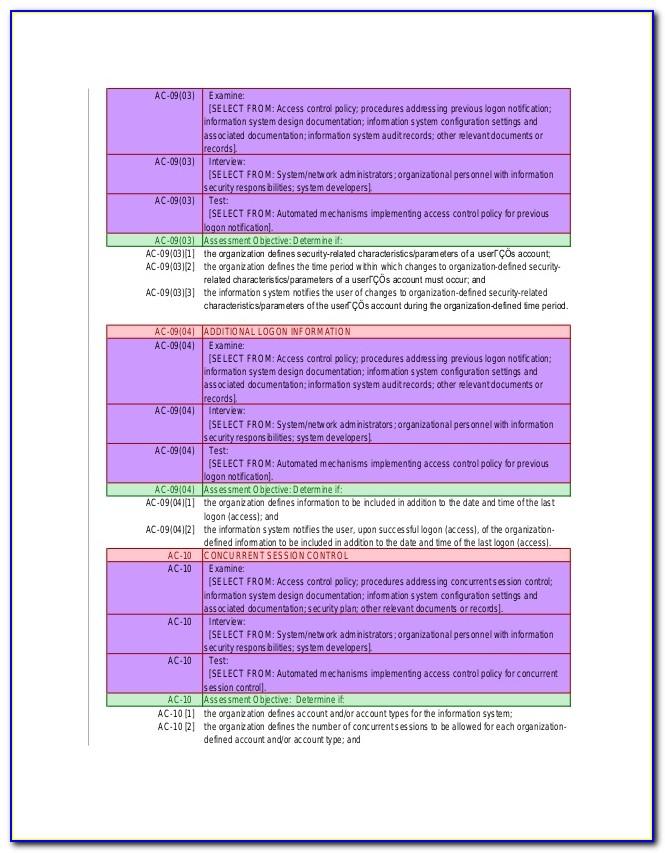
User Access Policy Template
User Access Policy Template - Authentication, authorization and claim issuance. The policy templates are provided courtesy of the state of new york and the state of california. All institution offices, campuses and learning centres 4.1.2. Users must only be provided with the absolute minimum access. The ad fs core pipeline for policy processing has three phases: • authentication credentials will not be coded into programs or queries. Why you need a remote access. The first and only privacy certification for. Latest bicep resource definition the vaults/accesspolicies resource type can be deployed to: The information security policy template that has been provided requires some areas to be filled in to ensure the policy is complete.
Standard Access Control Policy Template Free Download
Web download the access control policy template to provide procedures that prevent wanted and unwanted users from reading, modifying, or otherwise improperly using sensitive. Web we’ve put together this guide for you to understand how access control can help you gain greater control over your company’s data and the steps to set up your own. Authentication, authorization and claim issuance..
Provider Access Policy.pdf DocDroid
Why you need a remote access. Web we’ve put together this guide for you to understand how access control can help you gain greater control over your company’s data and the steps to set up your own. Web information security policy template. Web principle of least privilege access controls must be allocated on the basis of business need and ‘least.
Standard Access Control Policy Template Free Download
Why you need a remote access. All institution offices, campuses and learning centres 4.1.2. Web download the access control policy template to provide procedures that prevent wanted and unwanted users from reading, modifying, or otherwise improperly using sensitive. Web how to conduct a user access review step 1. Web what are access control policy templates?
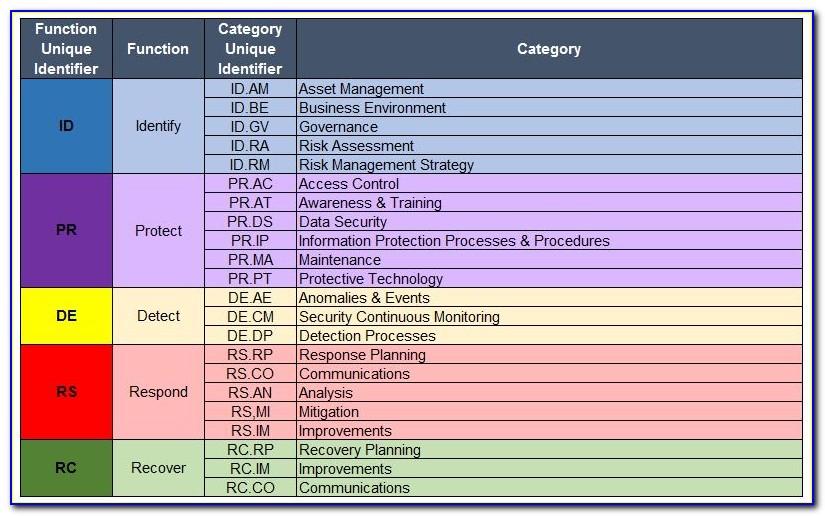
Nist 800 171 Access Control Policy Template
Web we’ve put together this guide for you to understand how access control can help you gain greater control over your company’s data and the steps to set up your own. • authentication credentials will not be coded into programs or queries. Web what are access control policy templates? Web download the access control policy template to provide procedures that.
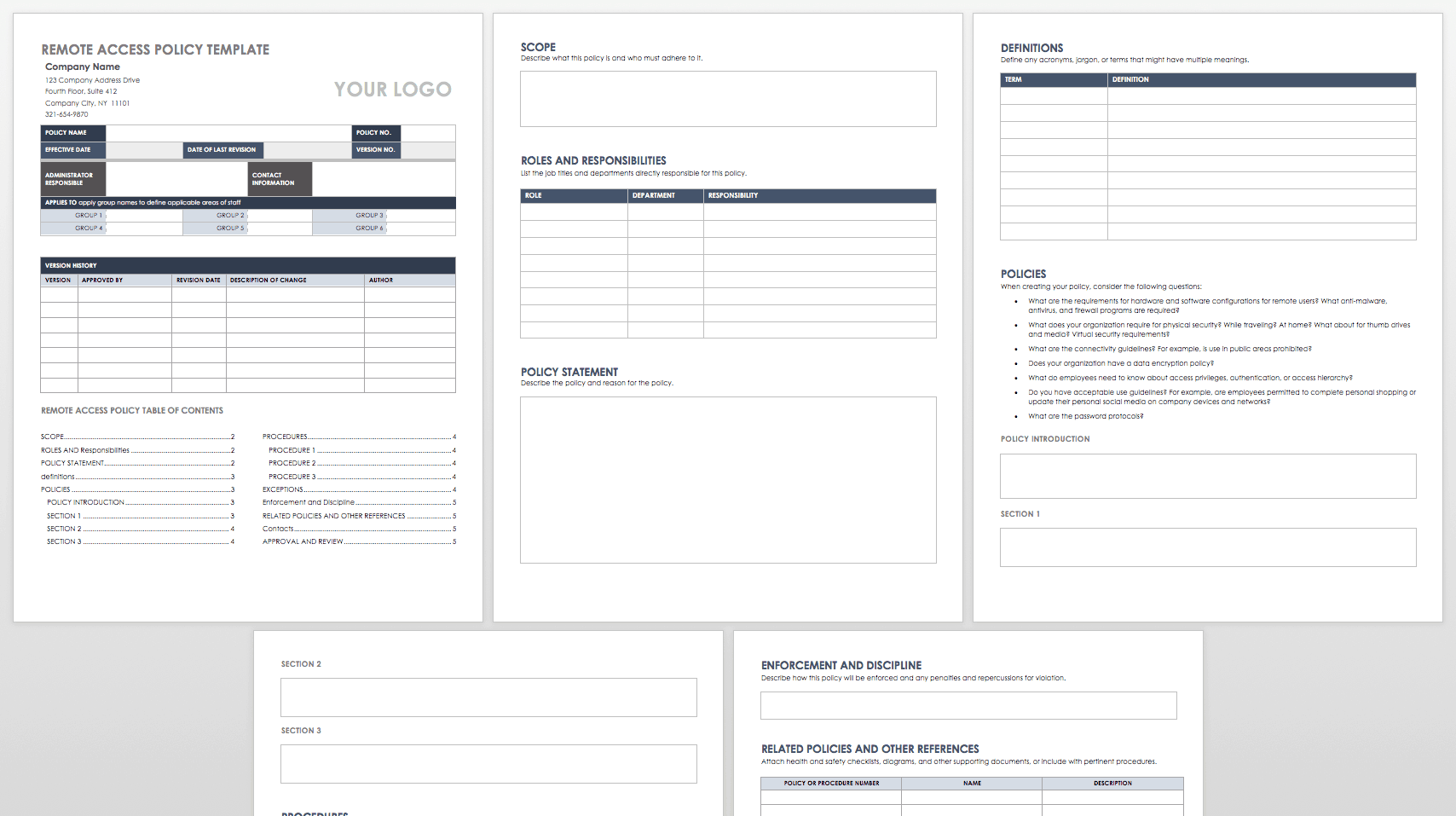
Remote Access Policy Template
Why you need a remote access. At minimum, a user access management policy should include the following: Define your user access policies. Web how to conduct a user access review step 1. • authentication credentials will not be coded into programs or queries.
Nist Access Control Policy Template
Web what are access control policy templates? The policy templates are provided courtesy of the state of new york and the state of california. All institution offices, campuses and learning centres 4.1.2. • authentication credentials will not be coded into programs or queries. Web overview adequate security of information and information systems is a fundamental management responsibility.
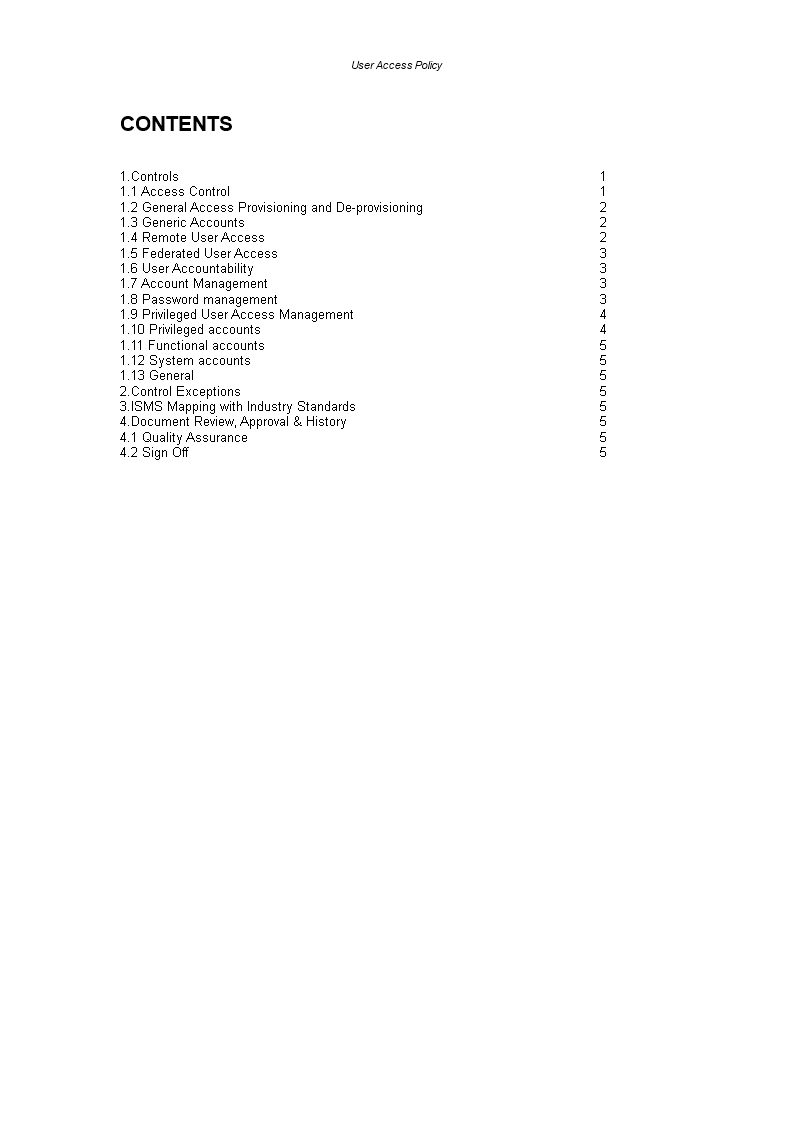
IT User Access Policy Templates at
The ad fs core pipeline for policy processing has three phases: Authentication, authorization and claim issuance. Web quickstart templates api versions: Before you start managing user access, it's crucial to establish clear policies and guidelines for granting and revoking access. Web how to conduct a user access review step 1.
Plantillas gratuitas de Políticas y procedimientos El Festival
Define your access management policy. Web all systems and applications must use encrypted authentication mechanisms and abide by the following: Why you need a remote access. All institution offices, campuses and learning centres 4.1.2. Web principle of least privilege access controls must be allocated on the basis of business need and ‘least privilege’.
IT User Access Policy Templates at
The first and only privacy certification for. Nearly all applications that deal with financial,. Web quickstart templates api versions: The ad fs core pipeline for policy processing has three phases: At minimum, a user access management policy should include the following:
3.5 Remote Access Policy
The first and only privacy certification for. Why you need a remote access. Authentication, authorization and claim issuance. All students, employees, consultants, contractors, agents and authorized users. Web overview adequate security of information and information systems is a fundamental management responsibility.
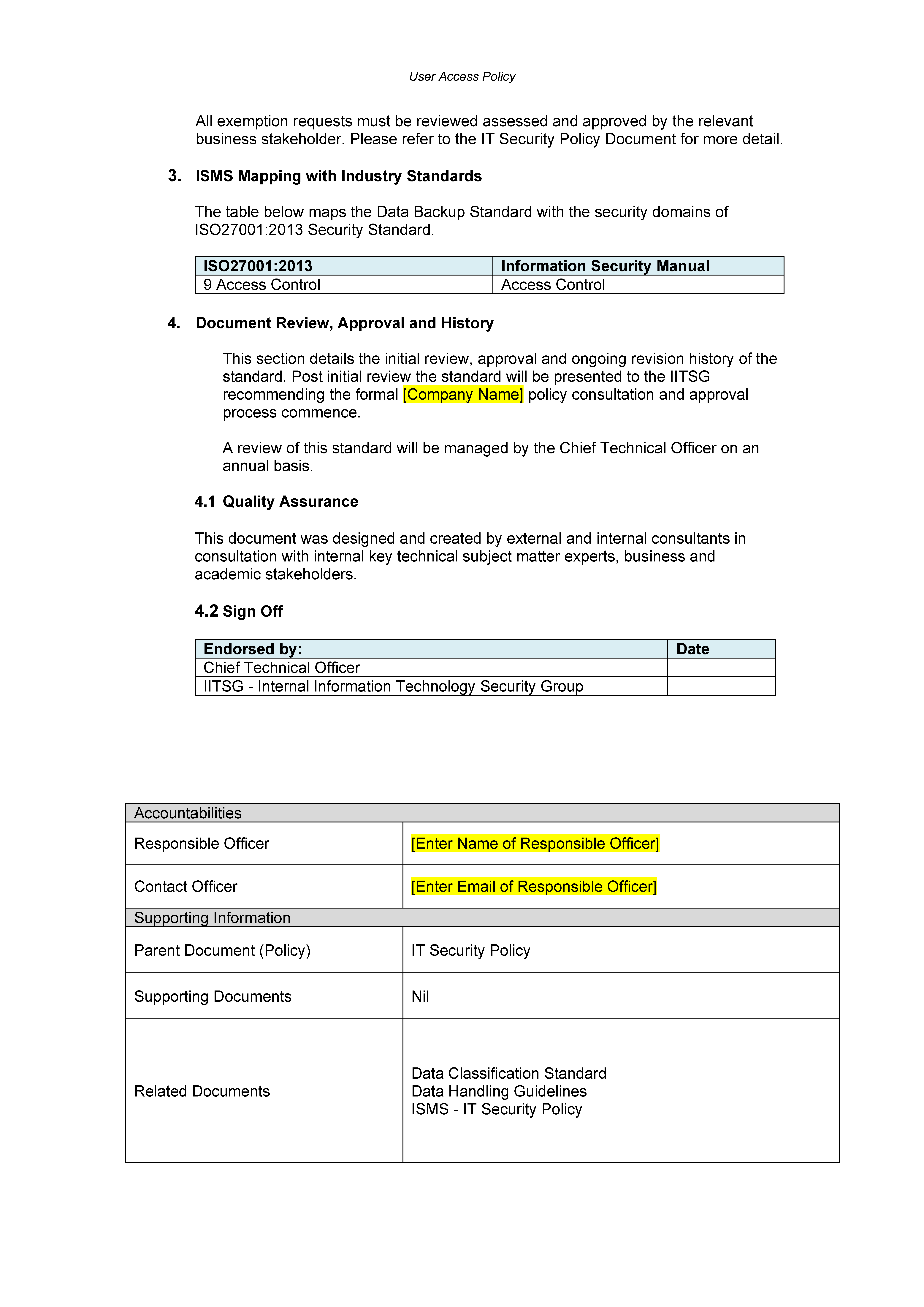
Web all systems and applications must use encrypted authentication mechanisms and abide by the following: Nearly all applications that deal with financial,. Web quickstart templates api versions: The information security policy template that has been provided requires some areas to be filled in to ensure the policy is complete. Web download the access control policy template to provide procedures that prevent wanted and unwanted users from reading, modifying, or otherwise improperly using sensitive. Why you need a remote access. Web what are access control policy templates? Latest bicep resource definition the vaults/accesspolicies resource type can be deployed to: • authentication credentials will not be coded into programs or queries. Web use the free, downloadable remote access security policy template included below to help prepare and document your organization's policy. Authentication, authorization and claim issuance. Before you start managing user access, it's crucial to establish clear policies and guidelines for granting and revoking access. The policy templates are provided courtesy of the state of new york and the state of california. Web principle of least privilege access controls must be allocated on the basis of business need and ‘least privilege’. Web how to conduct a user access review step 1. At minimum, a user access management policy should include the following: Users must only be provided with the absolute minimum access. Web overview adequate security of information and information systems is a fundamental management responsibility. Define your access management policy. The templates can be customized and used as an outline of.