Vulnerability Tracking Spreadsheet Template
Vulnerability Tracking Spreadsheet Template - Most vulnerability data comes from scanners, though the most important vulnerability data often comes from humans. Web free vulnerability powerpoint templates. You may also see simple form templates. Download this whitepaper to get: Web creating and implementing an vulnerability management policies and procedures is a vital component of any company’s cyber security strategy, and is required by several standards including: Web in this article, you’ll find the most effective cybersecurity risk assessment templates for project managers, security analysts, security incident responders, intrusion detection personnel, vulnerability assessors, and cryptologists. Web to use the vulnerability ranking spreadsheet follow these steps: In this blog post, we gathered all the necessary information you must have in regards to this topic. (remember that each pca is listed 4 times). For more information, see the fedramp product offering.
Free Vulnerability Assessment Templates Smartsheet
In this article, you’ll find the most comprehensive selection of free vulnerability assessments, available in microsoft excel and word, pdf, and google sheets formats. (remember that each pca is listed 4 times). This tool will allow you to track vulnerabilities from the point when they were identified to when they are remediated. You may also see simple form templates. Free.
Vulnerability Tracking Spreadsheet for Vulnerability Management Metrics
Track, prioritise, and remediate vulnerabilities for robust information security. The purpose of the controlcase vulnerability management policy and procedures templates are to. Web to help solve this problem, we put together a list of techniques and tools you can use for vulnerability management tracking. (remember that each pca is listed 4 times). Free vulnerability assessment report sample
Vulnerability Tracking Spreadsheet inside Vulnerability Tracking
The discovery of vulnerabilities and the analysis of pertinent vulnerabilities. Free company profile presentation template with slide layouts like about us, meet the team slide, quote slide and what we do slide. Web every vulnerability should follow this template. 7 requirements for vulnerability management tracking systems ; Be sure you don’t put [attacks] or [controls] in this category.
Vulnerability Tracking Spreadsheet in Outstanding Remediations Tracking
The discovery of vulnerabilities and the analysis of pertinent vulnerabilities. No matter how carefully planned or implemented, each security measure has its own vulnerable spots. On the new sheet, delete rows for any pcas that do not exist in any of the zones. Ad manage all your business expenses in one place with quickbooks®. (remember that each pca is listed.
Vulnerability Tracking Spreadsheet Spreadsheet Downloa vulnerability
Tenable vulnerability management provides a selection of report templates and customizable. Web learn how to use a penetration testing report template to document and track the remediation of the vulnerabilities you identify in your systems, networks, or applications. Web vulnerability remediation tracking is one of the important components of cyber security practices. Web to help solve this problem, we put.
Vulnerability Tracking Spreadsheet pertaining to Excel Spreadsheet
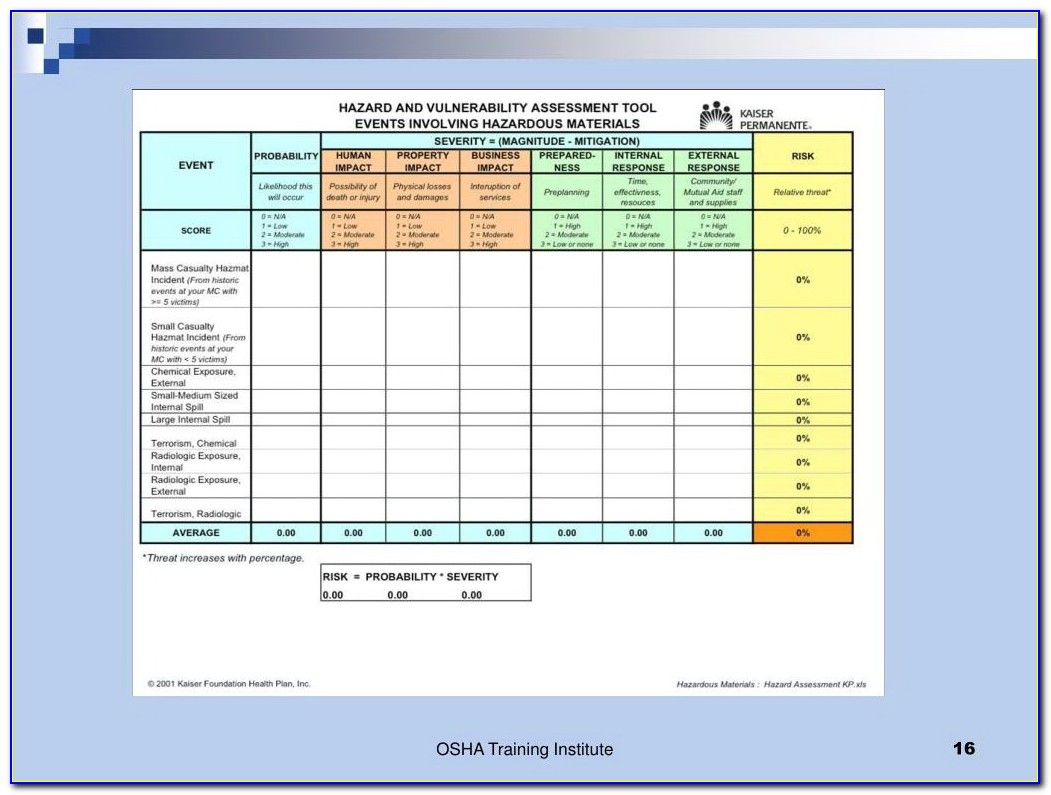
A vulnerability is a weakness in an application (frequently a broken or missing control) that enables an attack to succeed. Tenable vulnerability management provides a selection of report templates and customizable. Web the pram is a tool that applies the risk model from nistir 8062 and helps organizations analyze, assess, and prioritize privacy risks to determine how to respond and.
Vulnerability Tracking Spreadsheet for Debt Management Spreadsheet And
Download get, customizable vulnerabilities assessment templates, available into excel, word, pdf, and google sheets formats. Be sure you don’t put [attacks] or [controls] in this category. You may also see simple form templates. Web to use the vulnerability ranking spreadsheet follow these steps: On the new sheet, delete rows for any pcas that do not exist in any of the.
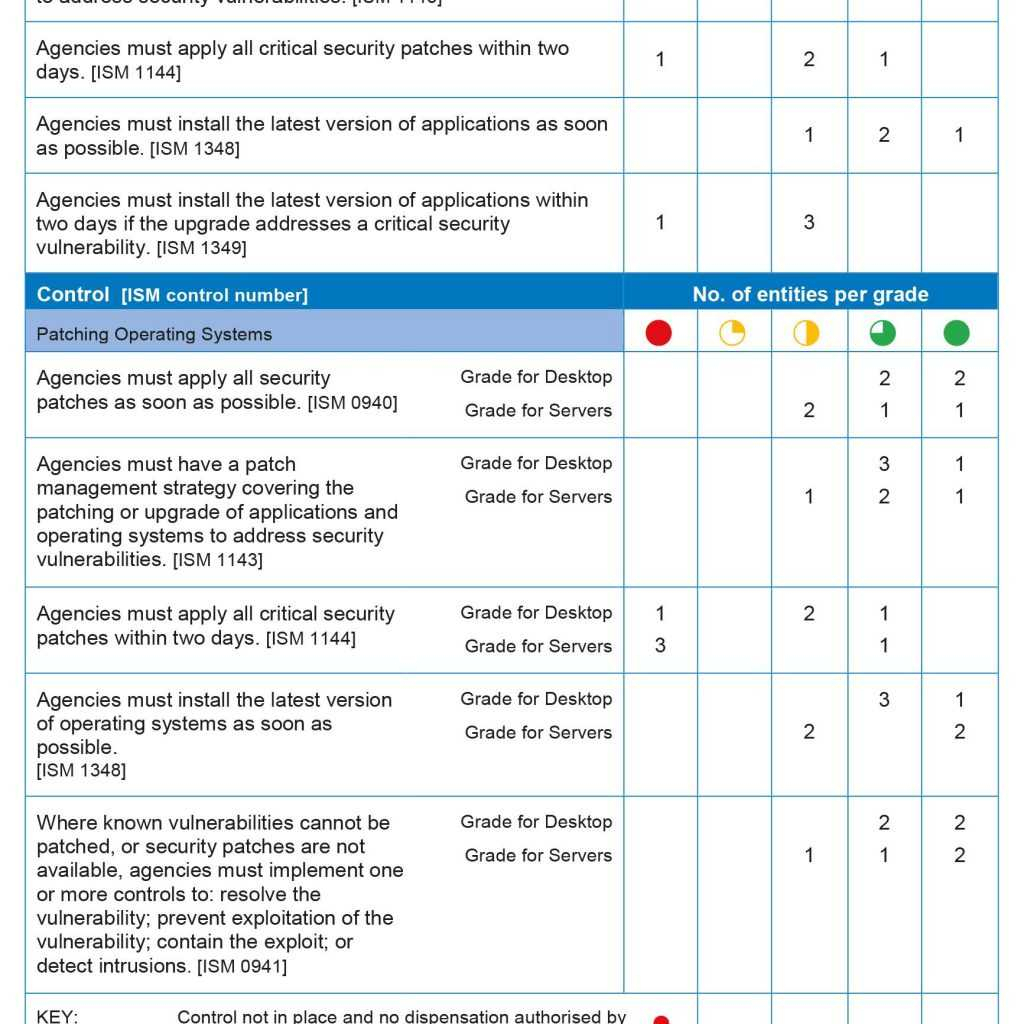
Patch Management Spreadsheet within Network Vulnerability Assessment
In this article, you’ll find the most comprehensive selection of free vulnerability assessments, available in microsoft excel and word, pdf, and google sheets formats. Tips and resources to help improve any vulnerability management. Web to help solve this problem, we put together a list of techniques and tools you can use for vulnerability management tracking. Make a copy of the.
Web Vulnerability Assessment Report Template Template Resume
Web vulnerability management requires an organization to understand and assess two specific capabilities: Download this whitepaper to get: Track, prioritise, and remediate vulnerabilities for robust information security. The following feature is not supported in tenable vulnerability management federal risk and authorization management program (fedramp) environments. Free vulnerability assessment report sample
Vulnerability Tracking Spreadsheet Spreadsheet Downloa vulnerability
Tenable vulnerability management provides a selection of report templates and customizable. Web any articles, templates, or information provided by smartsheet on the website are for reference only. Both spreadsheets have been preformatted for improved data visualization and allow for alternative views of the catalog. Provides penalties for failure to comply with this policy 7 requirements for vulnerability management tracking systems.
Most vulnerability data comes from scanners, though the most important vulnerability data often comes from humans. Free vulnerability assessment report sample The purpose of the controlcase vulnerability management policy and procedures templates are to. 7 requirements for vulnerability management tracking systems ; For more information, see the fedramp product offering. Track, prioritise, and remediate vulnerabilities for robust information security. Web in this article, you’ll find the most effective cybersecurity risk assessment templates for project managers, security analysts, security incident responders, intrusion detection personnel, vulnerability assessors, and cryptologists. Web to help solve this problem, we put together a list of techniques and tools you can use for vulnerability management tracking. Web get free smartsheet templates. Web free vulnerability powerpoint templates. Web any articles, templates, or information provided by smartsheet on the website are for reference only. Ad manage all your business expenses in one place with quickbooks®. On the new sheet, delete rows for any pcas that do not exist in any of the zones. No matter how carefully planned or implemented, each security measure has its own vulnerable spots. Each template is fully customizable, so you can tailor your assessment to your business needs. In this blog post, we gathered all the necessary information you must have in regards to this topic. Web the pram is a tool that applies the risk model from nistir 8062 and helps organizations analyze, assess, and prioritize privacy risks to determine how to respond and select appropriate solutions. Tips and resources to help improve any vulnerability management. (remember that each pca is listed 4 times). Defines reports to verify compliance with this policy;